This post is part of a series.
Part 1 – The basics
Part 2 – Lifecycle Management and Provisioning/Deprovisioning
Part 3 – RBAC/ABAC, Entitlements Management, and Requests & Approvals
Part 4 –Separation of Duties, Certification / Attestation, and Privileged Access Management (this post)
Separation of Duties
SoD is sometimes referred to as ‘segregation of duties’. The typical example used for SoD is Accounts Payable and Accounts Receivable, because having access to both allows a single user to intentionally or unintentionally commit fraud and cover it up. This concept of checks and balances goes hand in hand with the concept of least privilege, which is imperative to enforce security policies for data access. Using SoD rules or policies when defining roles and entitlements is essential to prevent or limit the likelihood of a single user’s ability to negatively impact our systems. These policies not only protect the users from making mistakes, but they also limit how much damage an intruder can make if they are able to impersonate that user. SoD rules and policies ideally should be preventative measures. A good identity governance solution should provide the means to enforce these policies during the access request and approval process.
Azure AD currently offers this feature in preview. You can add specific incompabible access packages:

Or specific incompatible groups:

This means that if the user already has the incompatible access package assigned, or is a member of the incompatible group, then they cannot request this access package.
Certification / Attestation
We couldn’t possibly talk about access without mentioning access reviews. Because no process is ever perfect, including the JML process, we need to certify or confirm access. Access reviews are typically part of the Identity Governance solution and the purpose is to certify privileges a user is assigned are still required by the user. There are two main parts to the UAR process:
- Reviewers, who are typically the LOB owners for those privileges, review the users that are assigned and either approve or deny the access going forward.
- The privileges are automatically removed for any users who were denied by the reviewers.

Azure AD also offers options to send notifications and reminders to the reviewers to ensure they provide feedback within the allotted time. There are also options to automatically remove the access on denied or not reviewed outcomes, basically for anything that wasn’t specifically approved by a person.

Continuous access reviews for privileged access group membership and privileged role assignments are essential to re-certify, attest, and audit users’ access to resources.
Azure AD offers access reviews for:
- Access Packages
- Teams/Groups and Applications
- Privileged roles and groups managed via PIM (see next section)
Privileged Access Management / Privileged Identity Management
Privileged roles are at the top of the priority goals for attackers, that’s why they have to be protected with an equivalent urgency level. Microsoft has done a fantastic job of documenting recommendations to protect privileged users, especially when it comes to protecting those highly privileged users from on-prem attacks.
Azure AD offers Privileged Identity Management which provides the ability to assign privileged roles either active or eligible. This means that if a user doesn’t need access for their daily job, they can then be assigned that role as eligible, which means they have to activate it when they need to use it. That activation can then require additional requirements, such as:
- Azure MFA
- Justification for activation
- Ticket – if a support ticket is required for auditing purposes
- Approval

As you can see above, the activation can also be restricted to only a certain number of hours, and it can be scheduled. So, if someone is expecting to work on a Saturday morning, they can get their approvals earlier in the week and schedule the activation for the hours they plan to work.
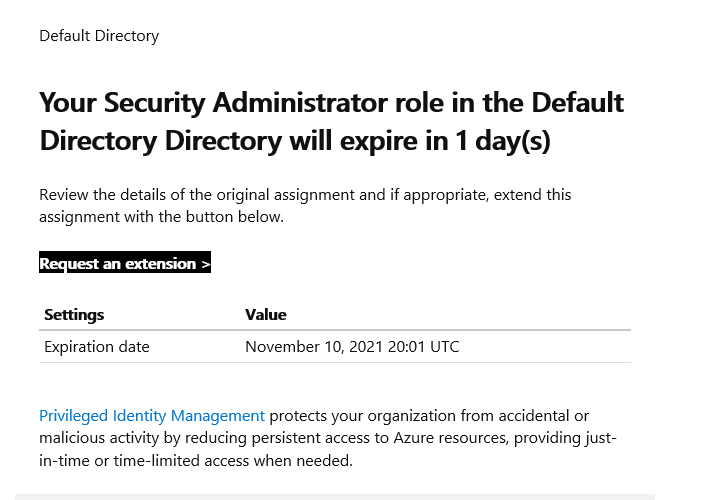
Another great feature is the ability to expire those role assignments. Many times privileged roles are assigned for a specific project and sometimes in an emergency situation and there’s really no need for those users to keep the roles forever.
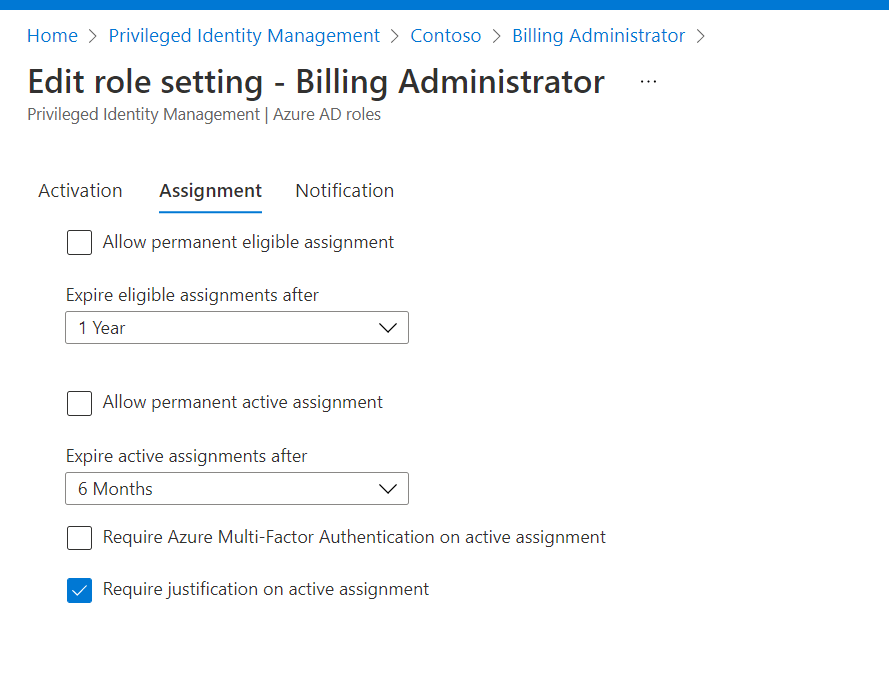
In this case PIM allows the assignments to expire and the users can then request extensions if they still need the roles.
Azure AD PIM currently supports the following groups and roles:
- Azure AD roles
- Azure resources (RBAC roles for subscriptions)
- Privileged access groups (preview), these are groups that can be assigned roles and have enabled privileged access.
Finally, one of my favorite features of PIM are the email notifications to ensure that once you implement PIM the assignments remain within the guidelines the enterprise has deemed necessary. The users that are assigned Global Administrator, Security Administrator, and Privileged Role Administrator will receive these notifications.

These administrators will be able to see if users are assigned roles outside PIM and/or assigned permanently, and they are provided with links to adjust the assignments as needed.
There is a LOT more to identity governance, but hopefully I have given you an idea of what an enterprise level solution should include and the tools that Azure AD provides to build on top of the robust solutions offered. On the road to implementing zero trust solutions, establishing a solid JML process is a big step forward for any enterprise. I know it’s called ‘governance’, but it’s much more than governance, it’s preventive security.
2 thoughts on “Joiners – Movers – Leavers (JML) Part 4”