This post is a part of a series.
- Part 1 – The basics
- Part 2 – About scopes or permissions and MSAL
- Part 3 – App Gallery and publisher verification (this post)
- Part 4 – Additional Security Features
Whether you are building something as complex as a SCIM connector or a mobile application, or just a simple SPA application, chances are you want to share your application with customers or other partners. If so, there are a few security features you should be aware of.
Publisher Verification
In part 2 I discussed the concept of consent and I briefly mentioned that organizations can control how and who can consent to the various permissions by updating the tenant settings. Well, those settings can be found here:
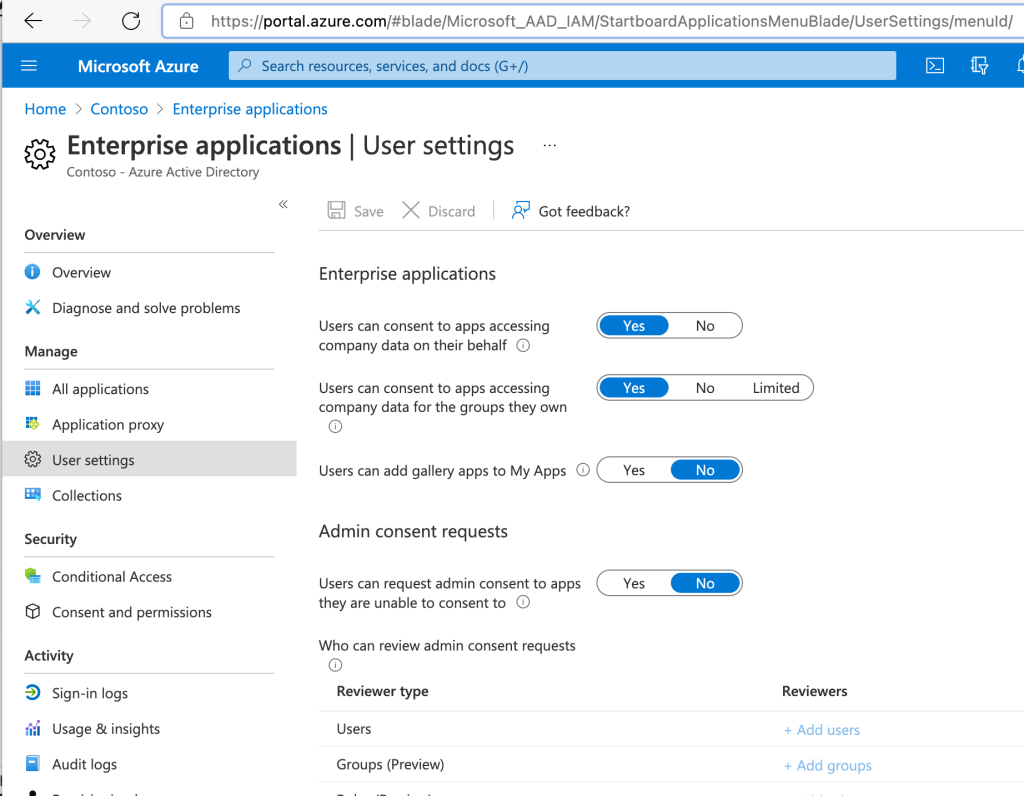
With the setting above organizations can prevent the users from being able to consent to share their data, and they can also configure a workflow that allows the users to request the consent from their administrators.
With the settings below organizations can allow end-users to consent to specific privileges they deem to be low impact only from verified publishers.
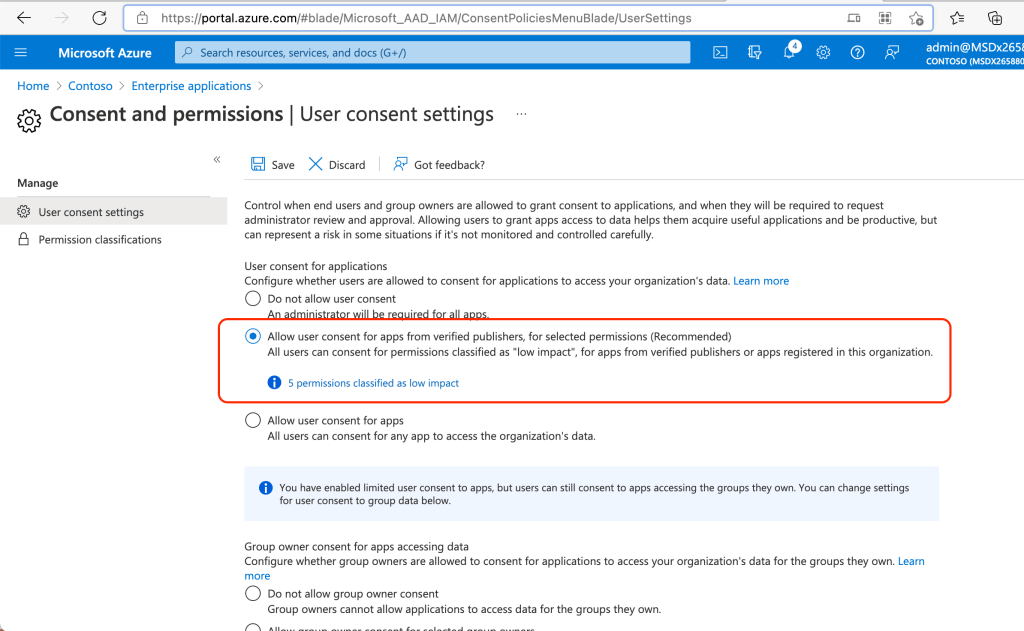
“Microsoft recommends restricting user consent to allow users to consent only for app from verified publishers, and only for permissions you select.” This is due to known risks associated with the abuse of application permissions that have either been forgotten by the organizations or simply not secured enough.
But what are verified publishers? Applications that are associated with a verified publisher provide the end-users with a trust factor. This is because becoming a verified publisher means the partner has a valid MPN (Microsoft Partner Network) account that has been verified to be a legitimate business. Once the process is completed any consent forms presented to users for applications associated with that MPN will show the verified publisher blue badge.
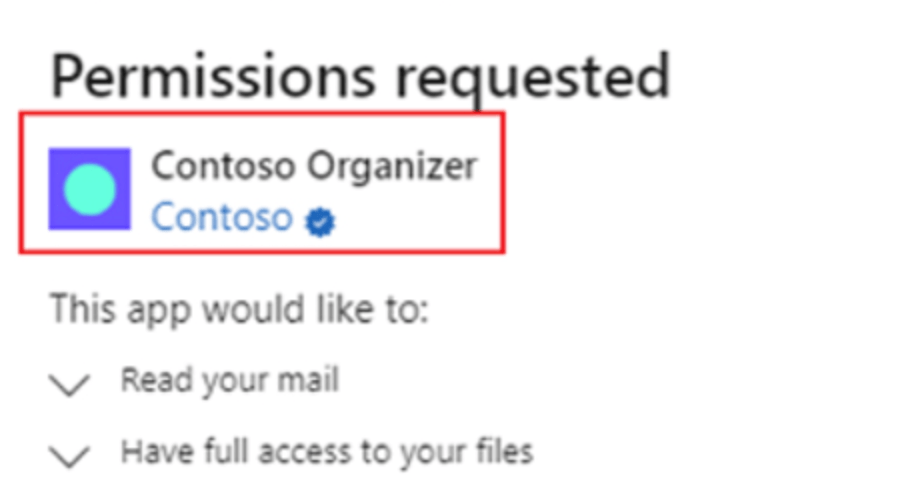
And as you can see above, it can also expedite the consent process if the tenants have the recommended settings that allow end-users to consent only for applications from a verified publisher.
AppGallery
App Gallery is a “catalog of thousands of apps that make it easy to deploy and configure single sign-on (SSO) and automated user provisioning.” The nice thing about AppGallery is that you can make your app available to all your customers in a secure way via Enterprise Apps. Although offering SSO for your application is highly recommended for security reasons, you don’t necessarily need to have both SSO and user provisioning enabled, it could be one or the other, so maybe you can start with some features and then later add others.
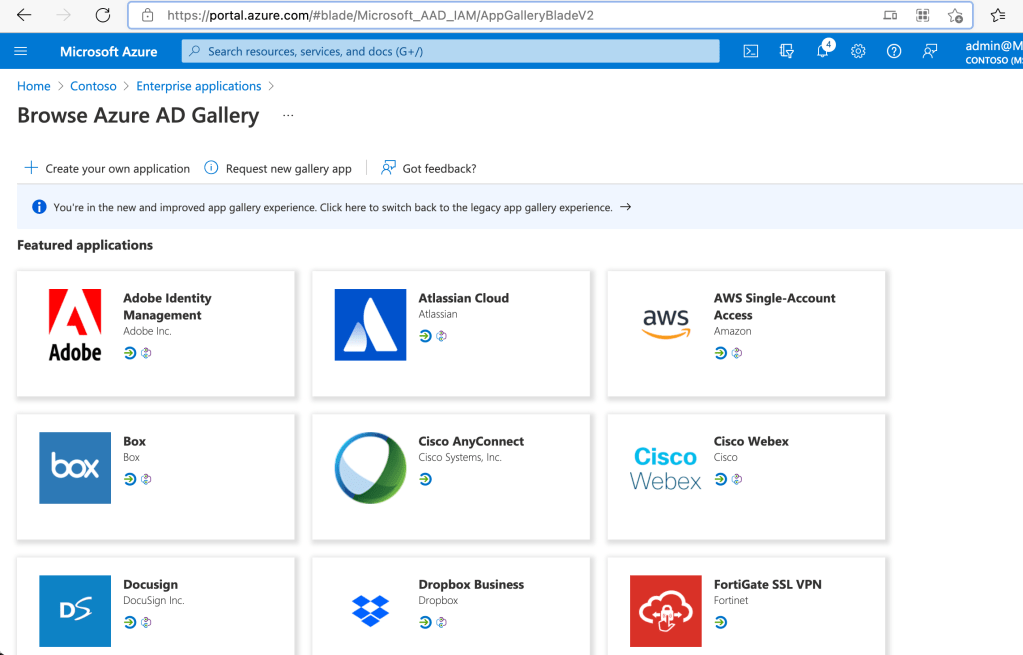
Keep in mind there is a process review associated with publishing your app via AppGallery, you can find the checklist and the steps here.
In part 4 of the series I’ll cover a few additional security recommendations for your custom applications.
4 thoughts on “Building secure applications using modern authentication (part 3)”