TL;DR – Yes, you can restrict file access within a folder. Keep reading to see how you can restrict downloads or other actions for specific files to only allow certain access from compliant devices.
This specific scenario came up during a session and I wanted to document and share how this is possible. The question was wether you could restrict downloads for specific files, not just at folder level, to only allow the download of that file on compliant devices. Yes, it’s possible!
It’s a real better together story, where the following services work together to deliver:
- Microsoft 365 Information Protection – for the sensitivity label configuration.
- Azure Active Directory Conditional Access – for the App Control within the sessions controls to enforce the policy on specific cloud apps and/or specific users. After detecting the signals, AAD forwards the evaluation to Defender for Cloud Apps.
- Microsoft Defender for Cloud Apps (previously MCAS) – for the conditional access policy that will evaluate the sensitivity labeled document is being downloaded from a compliant device, and if not, it will block it.
- Microsoft Endpoint Manager / Intune – for the compliance policies that determine if the device is compliant. Intune passes information about device compliance to Azure AD.
- Microsoft Defender for Endpoint – also helps because my compliance policies require devices to be at or under the specific risk score.
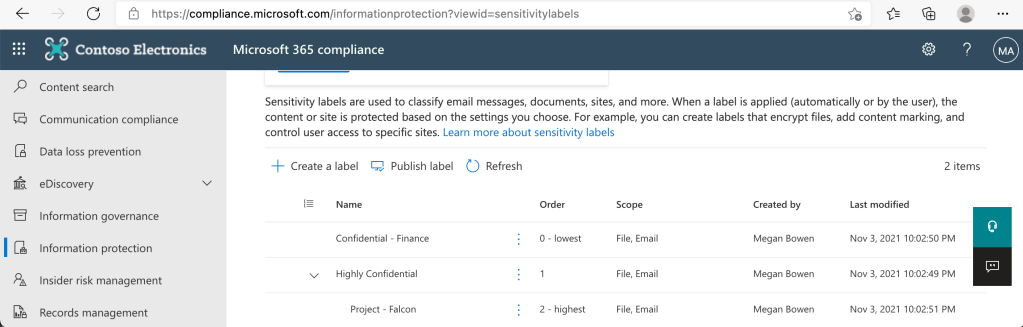
Information Protection Configuration
On this tenant I just have these three sensitivity labels with Highly Confidential – Project – Falcon being the highest level.
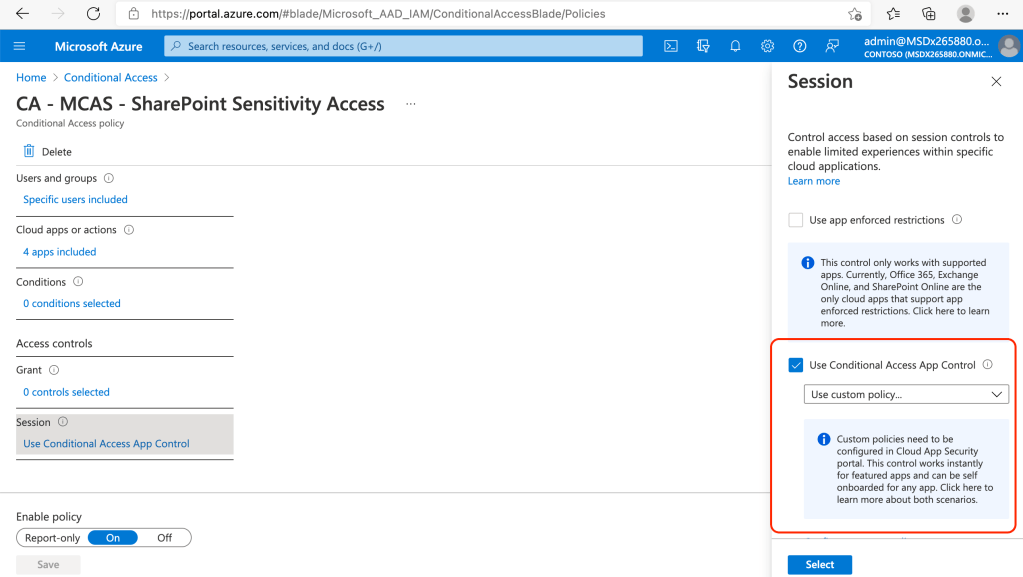
Azure Active Directory Conditional Access Configuration
This is the conditional access policy that will trigger the evaluation:

It will trigger for these specific cloud apps:

And it will then pass the baton over to Defender for Cloud Apps (previously MCAS) by selecting to “Use Conditional Access App Control” within Session controls.
Defender for Cloud Apps Configuration
In Defender for Cloud Apps (previously MCAS), I have a Conditional access policy:

And the following settings were used to configure this policy:
- Session control type: Control file download (with inspection)
- Filters: Device Tag does not equal Intune Compliant…
- Filters: Sensitivity label equal Highly Confidential – Project – Falcon

Additionally under Actions, I have selected to Block and notify, and I also customized the message the user will see.

Finally, I configured an additional alert to my email, which can be an administrator email, if needed.

I should also note that once you have completed the setup for the conditional access policy, you’ll notice these apps will slowly start showing in Defender for Cloud Apps under “Connected apps“, specifically under “Conditional Access App Control apps“.

Microsoft Endpoint Manager Configuration
Intune manages my endpoints and as you can see I have some compliant and some that are not compliant based on the compliance policies applied to them.

The compliance policies also require the device to be at or under the machine risk score:

I have connected Microsoft Endpoint Management to Defender for Endpoint as shown below:

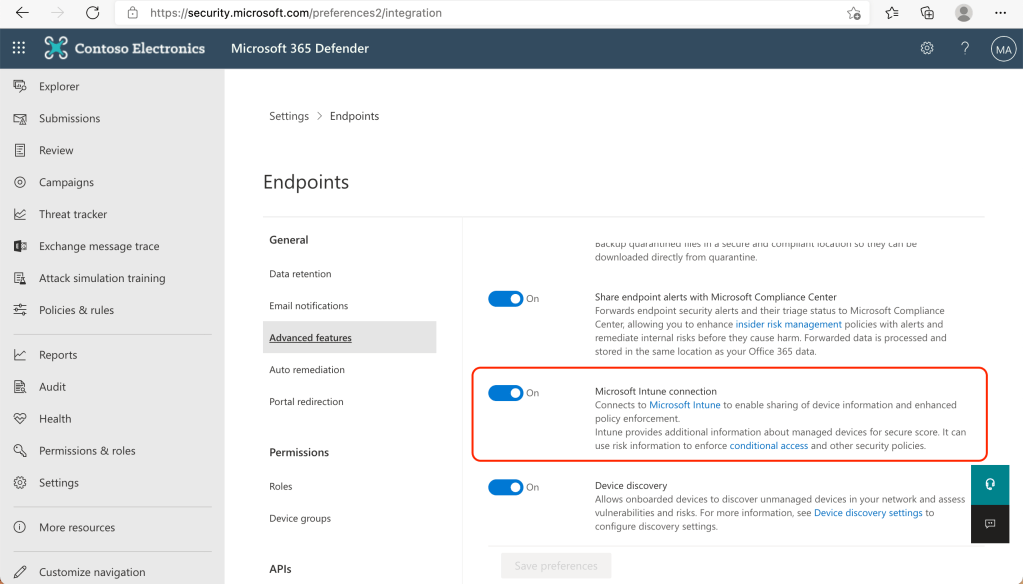
Defender for Endpoint Configuration
From the Defender for Endpoint side, I have also connected it to Intune to share device information:
Results
The final result is that any end user that tries to download files that are labeled Highly Confidential – Project – Falcon from a non-compliant device will be blocked, while still allowing downloads of other files in the same folder, as you can see this video:
The document that was blocked from downloading was labeled Highly Confidential – Project – Falcon and that is why the user is not allowed to download it to a non-compliant device.

Finally, since I configured an alert email, I also received this alert:

This is just one very specific scenario, there is so much more that is possible to modify and tweak depending on the requirements. However, I hope it gives you an idea of what is possible and hopefully inspires you to create your own scenario.
2 thoughts on “Restrict downloads for sensitive (confidential) documents to only compliant devices”